Can threat actors bypass DMARC?

Quick Answer
DMARC requires that an email pass either SPF or DKIM and align with the From domain; it does not require both. That or-condition is the gap attackers exploit. Three concrete bypass paths exist. First, the attacker sends from an IP inside the target's SPF record, usually by signing up for the same shared cloud email provider; the SPF check passes because the IP is technically authorized. Second, the attacker sends from a server that DKIM-signs outbound mail with the target's keys without checking who initiated the message; if the provider doesn't restrict DKIM key usage by tenant, the forged message gets a valid signature. Third, the attacker compromises the sender's device, mail server, or vendor mail server directly. The mitigations: pick email providers that scope SPF and DKIM per tenant, run DMARC at p=quarantine or p=reject so partial failures get blocked, monitor aggregate reports for unfamiliar sending sources, and tighten SPF ranges so shared IP blocks aren't a wide-open door. Misconfigured DMARC is worse than no DMARC because it implies enforcement that isn't actually there.

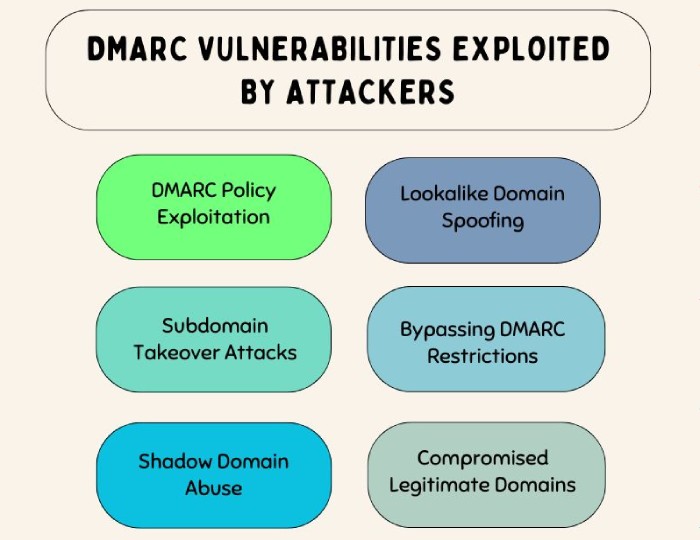
There is no doubt that DMARC is deployed to prevent phishing and spoofing emails; however, misconfigured DMARC records are synonymous with exploitable vulnerabilities. DMARC is implemented in tandem with SPF and DKIM. This email authentication structure compensates for the drawbacks of SPF and DKIM. SPF’s drawback is that it is highly likely to break when emails are forwarded; this means when someone forwards a legitimate email, the receiving server will either mark it as spam or reject it. DKIM’s drawback is that it triggers false positives because of inadvertent message modifications.
For an email to pass DMARC authentication checks, it must pass either SPF or DKIM but does not necessarily need to pass both. This is exactly where threat actors use their evil tactics so that phishing emails sent by them bypass DMARC filters and land in recipients’ inboxes.
Why does DMARC matter?
Once DMARC is in place, it significantly reduces the likelihood of fraudulent emails being sent from a domain. Compared to using SPF or DKIM alone, DMARC is more effective at blocking simple spoofing attempts and basic phishing attacks. DMARC works by combining SPF and DKIM into a unified validation process, with a clear policy (such as reject or quarantine) when authentication fails.
DMARC is especially valuable for domain owners with weak SPF or DKIM configurations. It allows email servers to treat a message as legitimate as long as either SPF or DKIM passes, reducing the risk of false positives. This represents a major step forward in email security.
While DMARC is strongly recommended for all domain owners and email filtering systems, it’s crucial to ensure you manage and control all email sources sent on behalf of your domain.
Interestingly, DMARC can also create a unique risk, in certain cases, it can actually make a domain more vulnerable to advanced spoofing attempts by skilled attackers.
How do attackers bypass DMARC to send forged emails?
A threat actor can possibly send forged emails without triggering DMARC if-
- They are able to send it from an IP address that is allowed under the forged sender domain’s SPF policy. To do this, they need to use the same email provider as the sender.
- They send the email from one of the servers officially authorized by the DKIM for the domain. If the server doesn’t cross-check who initiated the message (which is the case with most servers), it signs the outbound email going through it with the proper DKIM keys. This way, the forged message looks legitimate.
If an attacker creates an account with the same email provider as the legitimate domain, and that provider doesn’t restrict DKIM key usage, the attacker can send emails from the provider’s servers that appear properly signed, just like the real ones.
3. The malicious actor can compromise and access any sender’s devices or email servers. They can also compromise the vendor’s email servers.
But all this can be prevented if you delegate the email authentication responsibilities to experts. Please contact us to know how we can help you.
Topics

General Manager
General Manager at DuoCircle. Product strategy and commercial lead across the email security portfolio.
Secure your email infrastructure
Protect, authenticate, and deliver. Contact our team to find the right solution.