The point where DORA and DMARC meet

Quick Answer
DORA (the EU Digital Operational Resilience Act, in force January 17, 2023) and DMARC intersect because DORA requires financial entities, banks, insurers, investment firms, and their ICT third parties, to manage operational risk, report incidents, and prove resilience against digital disruptions, and email is the dominant attack vector. DMARC (Domain-based Message Authentication, Reporting and Conformance) builds on SPF and DKIM to tell receiving mailboxes how to handle messages claiming to come from your domain, with three policies: none (monitor), quarantine, or reject. Deploying DMARC at p=reject across all sending and parked domains cuts brand impersonation, reduces phishing risk to customers and counterparties, and produces aggregate reports that feed DORA's ICT risk management, incident reporting, and third-party oversight requirements. For DORA-scoped firms, DMARC is one of the cheapest, fastest controls that maps directly to multiple articles of the regulation.
The point where DORA and DMARC meet

Digital Operational Resilience Act (DORA) is a regulation by the European Union that came into force on January 17, 2023. It makes the financial institutions and entities within the finance sector more resilient towards fraud. It strengthens banks, insurance companies, investment firms, and other financial service providers to get back on their feet after major losses and disruptions.
Key components of DORA
Financial institutions are required to comply with the DORA provisions by a specified deadline. Although there are varied timelines for different requirements that you must check beforehand. Here are its critical elements–
ICT risk management
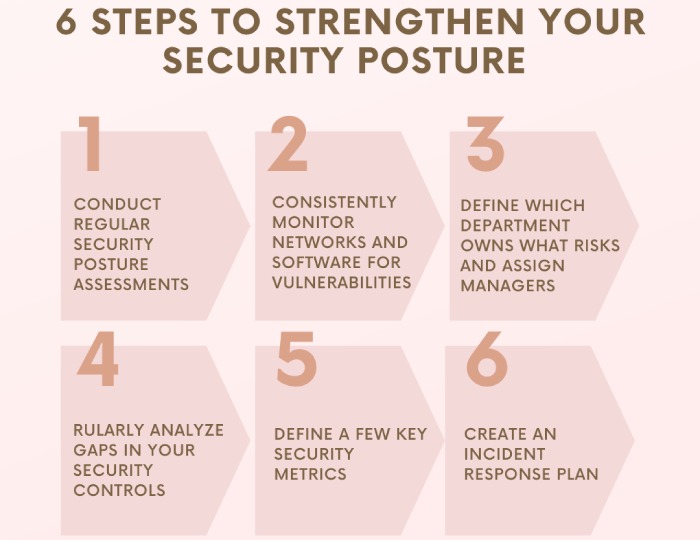
DORA requires financial sector organizations to have strong internal processes for managing Information and Communication Technology (ICT) risks. Some primary processes are regular and frequent risk assessments, monitoring, and response plans for ICT-related threats.
Incident reporting
Financial entities compliant with DORA are required to report major ICT-related disruptions and developments to the authorities as soon as possible. Delays are not appreciated. DORA has defined clear criteria for what is seen as a big incident that should be reported, and there are outlines of procedures that typically follow after it.
Testing
DORA requires financial entities to conduct regular testing of their ICT systems to ensure they can withstand cyberattacks and other digital disruptions. This includes vulnerability assessments, penetration testing, and scenario-based testing.
Third-party risk management
DORA wants the companies to also take care of the fact that third-party services used by them are also capable of managing risks. There are certain standards for operational resilience for them, and these shouldn’t be ignored.
Oversight
Supervisory authorities in the EU have enhanced powers to oversee and enforce the requirements of DORA. This includes the ability to impose sanctions on entities that fail to comply.
Information sharing
DORA encourages financial institutions and relevant authorities to share information related to cyber threats and vulnerabilities to improve the financial sector’s collective security posture.
What is DMARC?
DMARC stands for Domain-based Message Authentication Reporting and Conformance. It’s an email authentication protocol that is based on its predecessors, SPF and DKIM, for allowing the sending domain’s owner to instruct recipients’ mailboxes on how to deal with emails that claim to come from their domain but are actually unauthorized. DMARC users can command recipients’ mailboxes to either do nothing with emails that fail DMARC checks, place them in the spam folder, or reject their entry completely (also called bouncing back).
The intersection of DORA and DMARC
DMARC and DORA intersect by enhancing the security of financial institutions through robust email protection. By putting DMARC in place, you allow the detection of unauthorized email activities, reduce security vulnerabilities, and safeguard the business’s reputation. When phishing attempts and suspicious emails are flagged and quarantined, sensitive information is prevented from being exploited against email-based scams.
It also supports a comprehensive cybersecurity strategy by enabling the detection and response to fraudulent emails, ensuring secure communication in third-party contracts. Deploying DMARC across all domains provides extensive protection against phishing, spoofing, and ransomware attacks, aligning with DORA’s emphasis on operational resilience.
Topics

General Manager
General Manager at DuoCircle. Product strategy and commercial lead across the email security portfolio.
Secure your email infrastructure
Protect, authenticate, and deliver. Contact our team to find the right solution.